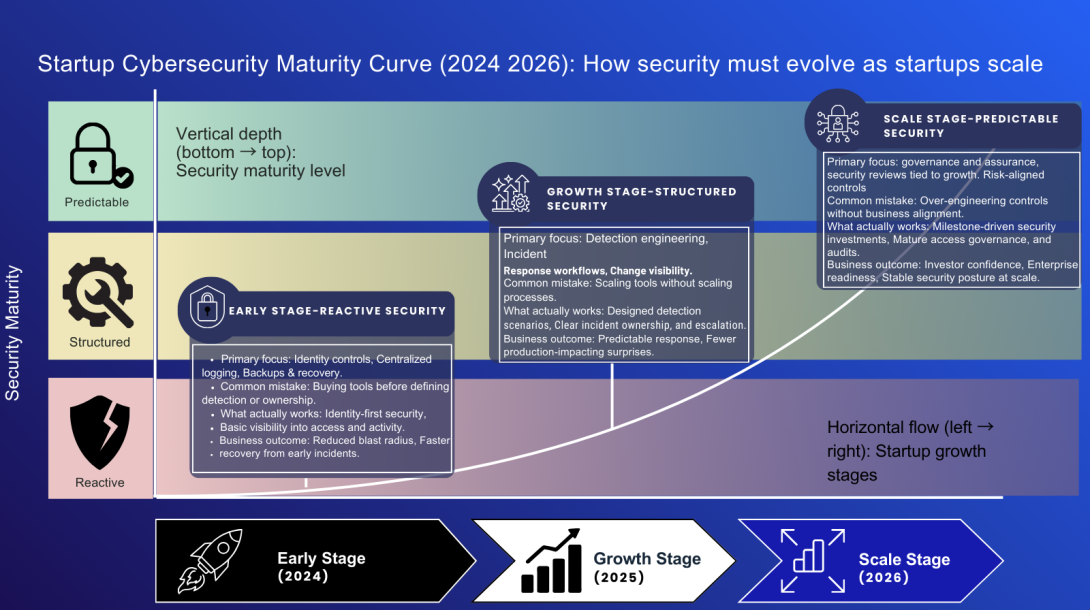
Most startups don’t struggle with cybersecurity because they ignore it. They struggle because they invest early, reactively, and without a clear operating model. Security budgets are often shaped by fear, compliance pressure, or vendor narratives—rather than by how risk actually materializes as a company grows.
As startups move toward 2026, this gap is becoming harder to ignore. Threats are faster, more automated, and more persistent. At the same time, customers, auditors, and investors expect security maturity much earlier than they did in the past. Buying more tools is no longer enough.
This article outlines five cybersecurity moves every startup should make before 2026—not as a checklist of controls, but as structural decisions that shape how security scales with the business. It covers why detection must be designed before tools are purchased, why identity—not the network—has become the primary security perimeter, and why incident response must be engineered into daily operations rather than documented once and forgotten.
The article also addresses a common blind spot in startup security programs: change velocity. Many breaches occur not because systems are unprotected, but because changes happen faster than teams can track or govern. Finally, it explains how security investments should align with business milestones, helping founders and technical leaders decide what to fund, what to delay, and how to avoid costly, reactive spending.
This is not an educational guide for beginners. It is a practical, experience-driven perspective for startups that want security to become a scalable operating discipline—rather than an expensive collection of tools that fails under pressure.

